搜索到
141
篇与
的结果
-
 python版本管理工具pyenv 项目地址https://github.com/pyenv/pyenv简介:python的版本管理工具:pyenv,他支持python多版本共存,并可以随时切换。且不会互相影响。centos7 安装pyenv:# 安装依赖 yum install zlib-devel bzip2-devel openssl-devel ncurses-devel sqlite-devel readline-devel tk-devel gdbm-devel db4-devel libpcap-devel xz-devel -y # 安装pyenv包 git clone https://github.com/pyenv/pyenv.git ~/.pyenv # 设置环境变量 vim ~/.bashrc export PYENV_ROOT="$HOME/.pyenv" export PATH="$PYENV_ROOT/bin:$PATH" eval "$(pyenv init -)" :wq 保存退出!# 刷新配置 source ~/.bashrc # 即是启动语句,重启系统执行这条语句 exec bash查看结果:pyenv -h Usage: pyenv <command> [<args>] Some useful pyenv commands are: commands List all available pyenv commands exec Run an executable with the selected Python version global Set or show the global Python version(s) help Display help for a command hooks List hook scripts for a given pyenv command init Configure the shell environment for pyenv install Install a Python version using python-build local Set or show the local application-specific Python version(s) prefix Display prefix for a Python version rehash Rehash pyenv shims (run this after installing executables) root Display the root directory where versions and shims are kept shell Set or show the shell-specific Python version shims List existing pyenv shims uninstall Uninstall a specific Python version version Show the current Python version(s) and its origin --version Display the version of pyenv version-file Detect the file that sets the current pyenv version version-name Show the current Python version version-origin Explain how the current Python version is set versions List all Python versions available to pyenv whence List all Python versions that contain the given executable which Display the full path to an executable See `pyenv help <command>' for information on a specific command. For full documentation, see: https://github.com/pyenv/pyenv#readme 安装成功~简单的介绍一下常用的命令:pyenv install --list //查看可安装的python版本 pyenv install 3.5.7 //安装python3.5.7 pyenv rehash //更新数据库,在安装 Python 或者其他带有可执行文件的模块之后,需要对数据库进行更新: pyenv versions //查看当前使用的python版本 pyenv global 3.5.7 //切换python全局版本为3.5.7 pyenv uninstall 3.5.7 //卸载已安装的python3.5.7某个目录指定版本[root@richerdyoung.com mnt]# pyenv global system #将当前的全局Python版本还原到之前的版本 [root@richerdyoung.com mnt]# python -V #系统自带的Python版本 Python 2.7.5 [root@richerdyoung.com mnt]# pyenv version #检查 pyenv当前py 版本 system (set by /root/.pyenv/version) [root@richerdyoung.com mnt]# mkdir ops #创建一个测试目录 [root@richerdyoung.com mnt]# cd ops/ [root@richerdyoung.com ops]# pyenv local 3.5.7 #使用local子命令指定当前目录使用3.5.7版本 [root@richerdyoung.com ops]# pyenv local # 确认是否设置成功 3.5.7 [root@richerdyoung.com ops]# python -V #检查当前版本 Python 3.5.7 [root@richerdyoung.com ops]# cd #切换到其他目录 [root@richerdyoung.com ~]# python -V #再次检查Python版本 ops目录下版本为3.5.7 全局为2.7.5 符合预期 Python 2.7.5ps : 当直接执行安装命令时候,国内会报错,error: failed to download Python-3.5.7.tar.zx解决办法:在当前用户目录下 .pyenv/ 目录下创建 cache 目录,将下载好的 Python-3.5.7 的包放在该目录下,就不会去下载Python文件,直接执行安装,而不需要下载,节省下载时间举例: # 我的目录是 /root/.pyenv # 则下载好的python包 存放 ~/.pyenv/cache/Python-3.5.7 ~/.pyenv/cache/Python-3.5.8
python版本管理工具pyenv 项目地址https://github.com/pyenv/pyenv简介:python的版本管理工具:pyenv,他支持python多版本共存,并可以随时切换。且不会互相影响。centos7 安装pyenv:# 安装依赖 yum install zlib-devel bzip2-devel openssl-devel ncurses-devel sqlite-devel readline-devel tk-devel gdbm-devel db4-devel libpcap-devel xz-devel -y # 安装pyenv包 git clone https://github.com/pyenv/pyenv.git ~/.pyenv # 设置环境变量 vim ~/.bashrc export PYENV_ROOT="$HOME/.pyenv" export PATH="$PYENV_ROOT/bin:$PATH" eval "$(pyenv init -)" :wq 保存退出!# 刷新配置 source ~/.bashrc # 即是启动语句,重启系统执行这条语句 exec bash查看结果:pyenv -h Usage: pyenv <command> [<args>] Some useful pyenv commands are: commands List all available pyenv commands exec Run an executable with the selected Python version global Set or show the global Python version(s) help Display help for a command hooks List hook scripts for a given pyenv command init Configure the shell environment for pyenv install Install a Python version using python-build local Set or show the local application-specific Python version(s) prefix Display prefix for a Python version rehash Rehash pyenv shims (run this after installing executables) root Display the root directory where versions and shims are kept shell Set or show the shell-specific Python version shims List existing pyenv shims uninstall Uninstall a specific Python version version Show the current Python version(s) and its origin --version Display the version of pyenv version-file Detect the file that sets the current pyenv version version-name Show the current Python version version-origin Explain how the current Python version is set versions List all Python versions available to pyenv whence List all Python versions that contain the given executable which Display the full path to an executable See `pyenv help <command>' for information on a specific command. For full documentation, see: https://github.com/pyenv/pyenv#readme 安装成功~简单的介绍一下常用的命令:pyenv install --list //查看可安装的python版本 pyenv install 3.5.7 //安装python3.5.7 pyenv rehash //更新数据库,在安装 Python 或者其他带有可执行文件的模块之后,需要对数据库进行更新: pyenv versions //查看当前使用的python版本 pyenv global 3.5.7 //切换python全局版本为3.5.7 pyenv uninstall 3.5.7 //卸载已安装的python3.5.7某个目录指定版本[root@richerdyoung.com mnt]# pyenv global system #将当前的全局Python版本还原到之前的版本 [root@richerdyoung.com mnt]# python -V #系统自带的Python版本 Python 2.7.5 [root@richerdyoung.com mnt]# pyenv version #检查 pyenv当前py 版本 system (set by /root/.pyenv/version) [root@richerdyoung.com mnt]# mkdir ops #创建一个测试目录 [root@richerdyoung.com mnt]# cd ops/ [root@richerdyoung.com ops]# pyenv local 3.5.7 #使用local子命令指定当前目录使用3.5.7版本 [root@richerdyoung.com ops]# pyenv local # 确认是否设置成功 3.5.7 [root@richerdyoung.com ops]# python -V #检查当前版本 Python 3.5.7 [root@richerdyoung.com ops]# cd #切换到其他目录 [root@richerdyoung.com ~]# python -V #再次检查Python版本 ops目录下版本为3.5.7 全局为2.7.5 符合预期 Python 2.7.5ps : 当直接执行安装命令时候,国内会报错,error: failed to download Python-3.5.7.tar.zx解决办法:在当前用户目录下 .pyenv/ 目录下创建 cache 目录,将下载好的 Python-3.5.7 的包放在该目录下,就不会去下载Python文件,直接执行安装,而不需要下载,节省下载时间举例: # 我的目录是 /root/.pyenv # 则下载好的python包 存放 ~/.pyenv/cache/Python-3.5.7 ~/.pyenv/cache/Python-3.5.8 -
 这56个代码注释让我笑喷了 1/* * Dear Maintainer * * Once you are done trying to ‘optimize’ this routine, * and you have realized what a terrible mistake that was, * please increment the following counter as a warning * to the next guy. * * total_hours_wasted_here = 73 */ 亲爱的维护者 如果尝试对这段程序进行'优化' 并且您已经意识到这是一个多么可怕的错误, 请增加以下计数器的个数用来对后来人进行警告 这里总共浪费的时间= 73 2. //Exception up = new Exception("Something is really wrong."); //throw up; //ha ha 例外=新的异常("确实有问题。") 放弃; //哈哈 3.// When I wrote this, only God and I understood what I was doing // Now, God only knows 当我写下这个的时候,只有上帝和我明白我在做什么 现在,只有上帝知道4.// sometimes I believe compiler ignores all my comments 有时,我会相信编译器会忽略我所有的注释5.// I dedicate all this code, all my work, to my wife, Darlene, // who will have to support me and our three children and // the dog once it gets released into the public. 谨以此代码,献给我的妻子达琳,感谢她一直支持着我,以及我的三个孩子和一条狗。6.// drunk, fix later 喝多了,改天再修7.// Magic. Do not touch. 魔法!不要碰。8.// I'm sorry. 抱歉。9.return 1; # returns 1 返回 1;# 返回 110. Catch (Exception e) { //who cares? } 捕获(异常e) 谁在乎? 11./** * Always returns true. */ public boolean isAvailable() { return false; } 代码返回 false ,注释则始终返回 true12./* * You may think you know what the following code does. * But you dont. Trust me. * Fiddle with it, and youll spend many a sleepless * night cursing the moment you thought youd be clever * enough to "optimize" the code below. * Now close this file and go play with something else. */ 你可能相信你能看懂以下代码, 但是其实绝对不可能,相信我。 一旦你调试了,你绝对会后悔装聪明去尝试优化这段代码。 最好的方式是关闭文件, 去玩点儿你喜欢的东西吧! 13.try { } finally { // should never happen } 绝对不会运行到这里14.const int TEN=10; // As if the value of 10 will fluctuate... 好像 10 的值会波动... 15.// This code sucks, you know it and I know it. // Move on and call me an idiot later. 这段代码的确很烂,我知道你也知道, 先不要骂我,请先接着往下看16.// If this comment is removed the program will blow up 如果删了此处注释,程序就炸了 17.// I am not responsible of this code. // They made me write it, against my will. 我不负责这个代码 他们强迫我写,违背了我的意愿。18./* Please work */ 请工作19. // no comments for you // it was hard to write // so it should be hard to read 没有注释, 很难写, 所以它应该很难阅读 20. options.BatchSize = 300; //Madness? THIS IS SPARTA! 疯了吧?这是斯巴达! 21.// If this code works, it was written by Paul DiLascia. // If not, I don't know who wrote it 如果这个代码能够正常工作,那么是Paul DiLascia写的 否则,我也不知道是谁写的22.// Peter wrote this, nobody knows what it does, don't change it! 这是彼得写的,没人知道它是做什么的,别改动!23. /** Logger */ private Logger logger = Logger.getLogger(); 不管怎么费尽心力,人会受伤的时候就会受伤。by 村上春树24.// I have to find a better job 我必须找到更好的工作25.// Real programmers don’t comment their code. // If it was hard to write, // it should be hard to understand. 真正的程序员不注释他们的代码。 如果很难写 应该是难以理解 26.// This is black magic // from // *Some stackoverlow link // Don’t play with magic, it can BITE. 这是来自stackoverlow的黑魔法 别玩魔法,它会咬人的27.// For the sins I am about to commit, may James Gosling forgive me 对于我即将犯下的罪行,希望詹姆斯·高斯林(James Gosling)能原谅我27.// Comment this later 稍后对此注释29.// Remove this if you wanna be fired 如果你想被炒鱿鱼,就删除它30. try{ }catch(Exception ex){ // Houston, we have a problem } Houston,我们有一个问题31.// I can’t divide with zero, so I have to divide with something very similar result = number / 0.00000000000001. 我不能除以0,所以我要除以一个非常相似的数32.int getRandomNumber() { Return 4; // chosen by fair dice roll. // guaranteed to be random. } 通过公平掷骰子选择 保证是随机的 33.#TODO: Figure out what I’m doing here and comment accordingly. 弄清楚这里做什么并相应地添加注释34.// If this code is still being used when it stops working, then // you have my permission to shoot me. Oh, you won't be able // to - I'll be dead... 如果这段代码停止工作时还在使用, 杀了我吧,哦~你不能这么做 我死了......35.// If you are reading this, that means you have been put in charge of my previous project. // I am sorry, so sorry for you. Godspeed. 如果你看到了这里,这意味着你已经被任命为我之前的项目的负责人。 对不起,真抱歉。祝你好运。36.// I wrote this while drunk, I don’t know what it does, // but if you remove it the program breaks. 我是在喝醉的时候写的,所以不知道它是干什么用的 但如果你删除它,程序就会中断37.// This code worked before, but my cat decided to take a // trip across my keyboard... 这段代码以前是有效的,但是我的猫决定在我的键盘上跑一趟38.long long ago; /* in a galaxy far far away */ 在很远很远的银河系外 (这段代码能运行,绝对是个奇迹)39.long john; // silver 金银岛.40.#define TRUE FALSE // Happy debugging suckers 快乐的去调试你的代码吧,哈哈41.// Dear future me. Please forgive me. // I can't even begin to express how sorry I am. 未来亲爱的我,请原谅我 我说不出来我有多抱歉42.// private instance variable for storing age public static int age; 用于存储年龄的私有实例变量43.// I am not sure why this works but it fixes the problem. 虽然我不知道为什么这样管用,但它却是修复了问题44.last = first; /* Biblical reference */ 最后即是开始,圣经引用45.try { } catch (SQLException ex) { // Basically, without saying too much, you're screwed. Royally and totally. } catch(Exception ex){ //If you thought you were screwed before, boy have I news for you!!! } 不用多说,基本上你完蛋了46.// John! If you'll svn remove this once more, // I'll shut you, for God's sake! // That piece of code is not "something strange"! // That is THE AUTH VALIDATION. 如果你再删除一次 看在上帝的份上,我要关闭你 这段代码不是什么“奇怪的东西” 那就是身份验证47.long time; /* know C */ 过来很久时间才知道48. // Abandon all hope ye who enter beyond this point 入此门者了断希望 49./* Ah ah ah! You'll never understand why this one works. */ 啊啊啊!你永远都不会明白为什么这个方法有效 50.try{ }catch (Ex as Exception) { // oh crap, we should do something. } 糟糕,我们应该做点什么51.// TODO make this work 用TODO做这件事 52.// If you're reading this, then my program is probably a success 如果你现在在认真详细的阅读这段代码,那么写的这段代码应该是没有问题的53.// set break point here - you'll never reach it 在这里设置断点-你永远作不到十全十美54./* ** The author disclaims copyright to this source code. ** In place of a legal notice, here is a blessing: ** ** May you do good and not evil. ** May you find forgiveness for yourself and forgive others. ** May you share freely, never taking more than you give. */ 作者放弃此源代码的版权 这是一份祝福,而不是法律通知 愿你行善不作恶。 愿你宽恕自己,宽恕他人 愿你自由分享,永远不要超过付出55.// I'm not sure what I did 我不确定我做了什么56.// This is crap code but it's 3 a.m. and I need to get this working. 这是垃圾代码,但现在是凌晨3点,我需要让他能够正常运行
这56个代码注释让我笑喷了 1/* * Dear Maintainer * * Once you are done trying to ‘optimize’ this routine, * and you have realized what a terrible mistake that was, * please increment the following counter as a warning * to the next guy. * * total_hours_wasted_here = 73 */ 亲爱的维护者 如果尝试对这段程序进行'优化' 并且您已经意识到这是一个多么可怕的错误, 请增加以下计数器的个数用来对后来人进行警告 这里总共浪费的时间= 73 2. //Exception up = new Exception("Something is really wrong."); //throw up; //ha ha 例外=新的异常("确实有问题。") 放弃; //哈哈 3.// When I wrote this, only God and I understood what I was doing // Now, God only knows 当我写下这个的时候,只有上帝和我明白我在做什么 现在,只有上帝知道4.// sometimes I believe compiler ignores all my comments 有时,我会相信编译器会忽略我所有的注释5.// I dedicate all this code, all my work, to my wife, Darlene, // who will have to support me and our three children and // the dog once it gets released into the public. 谨以此代码,献给我的妻子达琳,感谢她一直支持着我,以及我的三个孩子和一条狗。6.// drunk, fix later 喝多了,改天再修7.// Magic. Do not touch. 魔法!不要碰。8.// I'm sorry. 抱歉。9.return 1; # returns 1 返回 1;# 返回 110. Catch (Exception e) { //who cares? } 捕获(异常e) 谁在乎? 11./** * Always returns true. */ public boolean isAvailable() { return false; } 代码返回 false ,注释则始终返回 true12./* * You may think you know what the following code does. * But you dont. Trust me. * Fiddle with it, and youll spend many a sleepless * night cursing the moment you thought youd be clever * enough to "optimize" the code below. * Now close this file and go play with something else. */ 你可能相信你能看懂以下代码, 但是其实绝对不可能,相信我。 一旦你调试了,你绝对会后悔装聪明去尝试优化这段代码。 最好的方式是关闭文件, 去玩点儿你喜欢的东西吧! 13.try { } finally { // should never happen } 绝对不会运行到这里14.const int TEN=10; // As if the value of 10 will fluctuate... 好像 10 的值会波动... 15.// This code sucks, you know it and I know it. // Move on and call me an idiot later. 这段代码的确很烂,我知道你也知道, 先不要骂我,请先接着往下看16.// If this comment is removed the program will blow up 如果删了此处注释,程序就炸了 17.// I am not responsible of this code. // They made me write it, against my will. 我不负责这个代码 他们强迫我写,违背了我的意愿。18./* Please work */ 请工作19. // no comments for you // it was hard to write // so it should be hard to read 没有注释, 很难写, 所以它应该很难阅读 20. options.BatchSize = 300; //Madness? THIS IS SPARTA! 疯了吧?这是斯巴达! 21.// If this code works, it was written by Paul DiLascia. // If not, I don't know who wrote it 如果这个代码能够正常工作,那么是Paul DiLascia写的 否则,我也不知道是谁写的22.// Peter wrote this, nobody knows what it does, don't change it! 这是彼得写的,没人知道它是做什么的,别改动!23. /** Logger */ private Logger logger = Logger.getLogger(); 不管怎么费尽心力,人会受伤的时候就会受伤。by 村上春树24.// I have to find a better job 我必须找到更好的工作25.// Real programmers don’t comment their code. // If it was hard to write, // it should be hard to understand. 真正的程序员不注释他们的代码。 如果很难写 应该是难以理解 26.// This is black magic // from // *Some stackoverlow link // Don’t play with magic, it can BITE. 这是来自stackoverlow的黑魔法 别玩魔法,它会咬人的27.// For the sins I am about to commit, may James Gosling forgive me 对于我即将犯下的罪行,希望詹姆斯·高斯林(James Gosling)能原谅我27.// Comment this later 稍后对此注释29.// Remove this if you wanna be fired 如果你想被炒鱿鱼,就删除它30. try{ }catch(Exception ex){ // Houston, we have a problem } Houston,我们有一个问题31.// I can’t divide with zero, so I have to divide with something very similar result = number / 0.00000000000001. 我不能除以0,所以我要除以一个非常相似的数32.int getRandomNumber() { Return 4; // chosen by fair dice roll. // guaranteed to be random. } 通过公平掷骰子选择 保证是随机的 33.#TODO: Figure out what I’m doing here and comment accordingly. 弄清楚这里做什么并相应地添加注释34.// If this code is still being used when it stops working, then // you have my permission to shoot me. Oh, you won't be able // to - I'll be dead... 如果这段代码停止工作时还在使用, 杀了我吧,哦~你不能这么做 我死了......35.// If you are reading this, that means you have been put in charge of my previous project. // I am sorry, so sorry for you. Godspeed. 如果你看到了这里,这意味着你已经被任命为我之前的项目的负责人。 对不起,真抱歉。祝你好运。36.// I wrote this while drunk, I don’t know what it does, // but if you remove it the program breaks. 我是在喝醉的时候写的,所以不知道它是干什么用的 但如果你删除它,程序就会中断37.// This code worked before, but my cat decided to take a // trip across my keyboard... 这段代码以前是有效的,但是我的猫决定在我的键盘上跑一趟38.long long ago; /* in a galaxy far far away */ 在很远很远的银河系外 (这段代码能运行,绝对是个奇迹)39.long john; // silver 金银岛.40.#define TRUE FALSE // Happy debugging suckers 快乐的去调试你的代码吧,哈哈41.// Dear future me. Please forgive me. // I can't even begin to express how sorry I am. 未来亲爱的我,请原谅我 我说不出来我有多抱歉42.// private instance variable for storing age public static int age; 用于存储年龄的私有实例变量43.// I am not sure why this works but it fixes the problem. 虽然我不知道为什么这样管用,但它却是修复了问题44.last = first; /* Biblical reference */ 最后即是开始,圣经引用45.try { } catch (SQLException ex) { // Basically, without saying too much, you're screwed. Royally and totally. } catch(Exception ex){ //If you thought you were screwed before, boy have I news for you!!! } 不用多说,基本上你完蛋了46.// John! If you'll svn remove this once more, // I'll shut you, for God's sake! // That piece of code is not "something strange"! // That is THE AUTH VALIDATION. 如果你再删除一次 看在上帝的份上,我要关闭你 这段代码不是什么“奇怪的东西” 那就是身份验证47.long time; /* know C */ 过来很久时间才知道48. // Abandon all hope ye who enter beyond this point 入此门者了断希望 49./* Ah ah ah! You'll never understand why this one works. */ 啊啊啊!你永远都不会明白为什么这个方法有效 50.try{ }catch (Ex as Exception) { // oh crap, we should do something. } 糟糕,我们应该做点什么51.// TODO make this work 用TODO做这件事 52.// If you're reading this, then my program is probably a success 如果你现在在认真详细的阅读这段代码,那么写的这段代码应该是没有问题的53.// set break point here - you'll never reach it 在这里设置断点-你永远作不到十全十美54./* ** The author disclaims copyright to this source code. ** In place of a legal notice, here is a blessing: ** ** May you do good and not evil. ** May you find forgiveness for yourself and forgive others. ** May you share freely, never taking more than you give. */ 作者放弃此源代码的版权 这是一份祝福,而不是法律通知 愿你行善不作恶。 愿你宽恕自己,宽恕他人 愿你自由分享,永远不要超过付出55.// I'm not sure what I did 我不确定我做了什么56.// This is crap code but it's 3 a.m. and I need to get this working. 这是垃圾代码,但现在是凌晨3点,我需要让他能够正常运行 -
![微信支付报错dial tcp [240e:e1:a900:50::49]:443: connect: network is unreachable](https://static.richerdyoung.com/blog/image/lazyload.jpg)
-
 TP3.2框架中如何使用多个mysql函数 如FIND_IN_SET 和 !FIND_IN_SET 数据查询中可能会用到数据表中的多个字段去做匹配 可能会用到多个FIND_IN_SET 也可能需要拼接多个条件$user_ids = [1,2,3]; //获取需要匹配的值 if ($user_ids ){ foreach ($user_ids as $val){ $map[] = " FIND_IN_SET($val,show_user_id) "; } } $where['_string'] = implode(" OR ",$map); # 预览sql效果: WHERE FIND_IN_SET('1', show_user_id) OR FIND_IN_SET('2', show_user_id) OR FIND_IN_SET(3, show_user_id) 但是如果我们想除了这个函数还有其他函数要使用的时候并且$where['_string']已经被使用的时候怎么拼接? $where['_logic'] = 'or';//and 或者 OR 就是看你的需要 $map['_string'] = " !FIND_IN_SET(4,show_user_id) "; $where['_complex'] = $map; # 预览sql效果: WHERE FIND_IN_SET('1', show_user_id) OR FIND_IN_SET('2', show_user_id) OR FIND_IN_SET(3, show_user_id) AND ( ( !FIND_IN_SET(4, show_user_id) //就是与FIND_IN_SET相反的意思 ) )
TP3.2框架中如何使用多个mysql函数 如FIND_IN_SET 和 !FIND_IN_SET 数据查询中可能会用到数据表中的多个字段去做匹配 可能会用到多个FIND_IN_SET 也可能需要拼接多个条件$user_ids = [1,2,3]; //获取需要匹配的值 if ($user_ids ){ foreach ($user_ids as $val){ $map[] = " FIND_IN_SET($val,show_user_id) "; } } $where['_string'] = implode(" OR ",$map); # 预览sql效果: WHERE FIND_IN_SET('1', show_user_id) OR FIND_IN_SET('2', show_user_id) OR FIND_IN_SET(3, show_user_id) 但是如果我们想除了这个函数还有其他函数要使用的时候并且$where['_string']已经被使用的时候怎么拼接? $where['_logic'] = 'or';//and 或者 OR 就是看你的需要 $map['_string'] = " !FIND_IN_SET(4,show_user_id) "; $where['_complex'] = $map; # 预览sql效果: WHERE FIND_IN_SET('1', show_user_id) OR FIND_IN_SET('2', show_user_id) OR FIND_IN_SET(3, show_user_id) AND ( ( !FIND_IN_SET(4, show_user_id) //就是与FIND_IN_SET相反的意思 ) ) -
 微信小程序播放视频卡顿问题 一、默认初次加载卡顿情况明显微信小程序使用video组件播放视频的时候,会出现卡顿或者无法播放的问题,加一个custom-cache=”{{false}}“即可解决,这个属性文档上没有,是从小程序开发社区中get到的<video src="{{url}}" id="videoOne" custom-cache="{{false}}"> </video>二、视频卡顿,还有一种情况就是视频内容画面分辨率太大。解决方案:使用视频压缩工具,处理视频内容,建议720P就可以了。如果以上问题还不能解决。可以尝试提交代码片段给官方处理https://developers.weixin.qq.com/miniprogram/dev/devtools/minicode.html
微信小程序播放视频卡顿问题 一、默认初次加载卡顿情况明显微信小程序使用video组件播放视频的时候,会出现卡顿或者无法播放的问题,加一个custom-cache=”{{false}}“即可解决,这个属性文档上没有,是从小程序开发社区中get到的<video src="{{url}}" id="videoOne" custom-cache="{{false}}"> </video>二、视频卡顿,还有一种情况就是视频内容画面分辨率太大。解决方案:使用视频压缩工具,处理视频内容,建议720P就可以了。如果以上问题还不能解决。可以尝试提交代码片段给官方处理https://developers.weixin.qq.com/miniprogram/dev/devtools/minicode.html -
 【laravel】 操作文件上传 1、获取上传的文件$file=$request->file('file');2、获取上传文件的文件名(带后缀,如abc.png)$filename=$file->getClientOriginalName();3、获取上传文件的后缀(如abc.png,获取到的为png)$fileextension=$file->getClientOriginalExtension();4、获取上传文件的大小$filesize=$file->getClientSize();5、获取缓存在tmp目录下的文件名(带后缀,如php8933.tmp)$filaname=$file->getFilename();6、获取上传的文件缓存在tmp文件夹下的绝对路径$realpath=$file->getRealPath();7、将缓存在tmp目录下的文件移到某个位置,返回的是这个文件移动过后的路径$path=$file->move(path,newname);move()方法有两个参数,第一个参数是文件移到哪个文件夹下的路径,第二个参数是将上传的文件重新命名的文件名8、检测上传的文件是否合法,返回值为true或false$file->isValid()
【laravel】 操作文件上传 1、获取上传的文件$file=$request->file('file');2、获取上传文件的文件名(带后缀,如abc.png)$filename=$file->getClientOriginalName();3、获取上传文件的后缀(如abc.png,获取到的为png)$fileextension=$file->getClientOriginalExtension();4、获取上传文件的大小$filesize=$file->getClientSize();5、获取缓存在tmp目录下的文件名(带后缀,如php8933.tmp)$filaname=$file->getFilename();6、获取上传的文件缓存在tmp文件夹下的绝对路径$realpath=$file->getRealPath();7、将缓存在tmp目录下的文件移到某个位置,返回的是这个文件移动过后的路径$path=$file->move(path,newname);move()方法有两个参数,第一个参数是文件移到哪个文件夹下的路径,第二个参数是将上传的文件重新命名的文件名8、检测上传的文件是否合法,返回值为true或false$file->isValid() -
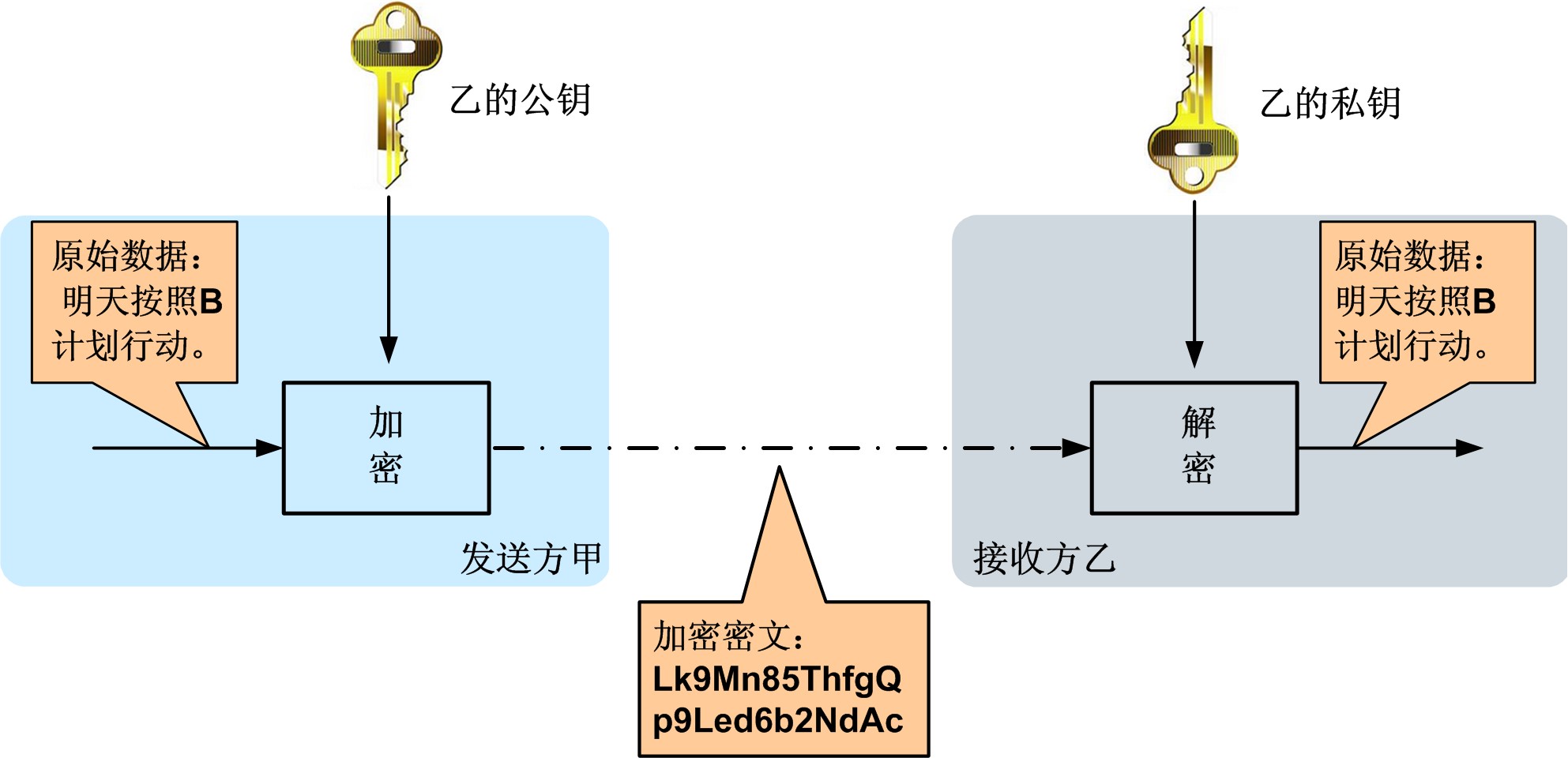
 【PHP】RSA非对称加密解密 PHP服务端与客户端交互或者提供开放API时,通常需要对敏感的数据进行加密,这时候rsa非对称加密就能派上用处了。举个通俗易懂的例子,假设我们再登录一个网站,发送账号和密码,请求被拦截了。密码没加密,那攻击者就直接拿到了密码,这是最搓的。密码加密了,是不可逆加密,那攻击者只需要模拟那个请求即可登录。密码加密了,是可逆加密,其中携带有时间等参数,后台可以根据时间等参数来判断是否有效,但因为是在前端加密,其加密方式也能在代码中找到,找到加密方式就可以得出解密方式。但是如果我们使用非对称加密就可以避免以上问题。非对称加密算法需要两个密钥来进行加密和解密,这两个秘钥是公开密钥(public key,简称公钥)和私有密钥(private key,简称私钥)。工作过程如下,甲乙之间使用非对称加密的方式完成了重要信息的安全传输。乙方生成一对密钥(公钥和私钥)并将公钥向其它方公开。得到该公钥的甲方使用该密钥对机密信息进行加密后再发送给乙方。乙方再用自己保存的另一把专用密钥(私钥)对加密后的信息进行解密。乙方只能用其专用密钥(私钥)解密由对应的公钥加密后的信息。在传输过程中,即使攻击者截获了传输的密文,并得到了乙的公钥,也无法破解密文,因为只有乙的私钥才能解密密文。同样,如果乙要回复加密信息给甲,那么需要甲先公布甲的公钥给乙用于加密,甲自己保存甲的私钥用于解密。在非对称加密中使用的主要算法有:RSA、Elgamal、背包算法、Rabin、D-H、ECC(椭圆曲线加密算法)等。下面我们通过一个例子来说明如何用PHP来实现RSA的加密解密。<?php class Rsa { public $privateKey = ''; public $publicKey = ''; public function __construct() { $resource = openssl_pkey_new(); openssl_pkey_export($resource, $this->privateKey); $detail = openssl_pkey_get_details($resource); $this->publicKey = $detail['key']; } public function publicEncrypt($data, $publicKey) { openssl_public_encrypt($data, $encrypted, $publicKey); return $encrypted; } public function publicDecrypt($data, $publicKey) { openssl_public_decrypt($data, $decrypted, $publicKey); return $decrypted; } public function privateEncrypt($data, $privateKey) { openssl_private_encrypt($data, $encrypted, $privateKey); return $encrypted; } public function privateDecrypt($data, $privateKey) { openssl_private_decrypt($data, $decrypted, $privateKey); return $decrypted; } } $rsa = new Rsa(); echo "公钥:\n", $rsa->publicKey, "\n"; echo "私钥:\n", $rsa->privateKey, "\n"; // 使用公钥加密 $str = $rsa->publicEncrypt('hello', $rsa->publicKey); // 这里使用base64是为了不出现乱码,默认加密出来的值有乱码 $str = base64_encode($str); echo "公钥加密(base64处理过):\n", $str, "\n"; $str = base64_decode($str); $pubstr = $rsa->publicDecrypt($str, $rsa->publicKey); echo "公钥解密:\n", $pubstr, "\n"; $privstr = $rsa->privateDecrypt($str, $rsa->privateKey); echo "私钥解密:\n", $privstr, "\n"; // 使用私钥加密 $str = $rsa->privateEncrypt('world', $rsa->privateKey); // 这里使用base64是为了不出现乱码,默认加密出来的值有乱码 $str = base64_encode($str); echo "私钥加密(base64处理过):\n", $str, "\n"; $str = base64_decode($str); $pubstr = $rsa->publicDecrypt($str, $rsa->publicKey); echo "公钥解密:\n", $pubstr, "\n"; $privstr = $rsa->privateDecrypt($str, $rsa->privateKey); echo "私钥解密:\n", $privstr, "\n"; 大家执行一下可以看到公钥加密的数据,只有私钥能解密,反之亦然,私钥加密的数据只有公钥能解码。这是PHP端的实现,可用在第三方跟平台之间的数据传输,但如果是前端传到后端该怎么办呢,搜索了一下,发现了这个库https://github.com/travist/jsencrypt使用jsencrypt加密解密的例子如下:<!DOCTYPE html> <html> <head> <title>JSEncrypt Example</title> <base id="basetag" href="/jsencrypt-2.3.0/"> <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <meta name="viewport" content="width=device-width, initial-scale=1.0"> <script src="jquery.js"></script> <script type="text/javascript" src="bin/jsencrypt.js"></script> </head> <body> <div class="container"> <script type="text/javascript"> // Call this code when the page is done loading. $(function() { // Run a quick encryption/decryption when they click. $('#testme').click(function() { // Encrypt with the public key... var encrypt = new JSEncrypt(); encrypt.setPublicKey($('#pubkey').val()); var encrypted = encrypt.encrypt($('#input').val()); console.log(encrypted) // Decrypt with the private key... var decrypt = new JSEncrypt(); decrypt.setPrivateKey($('#privkey').val()); var uncrypted = decrypt.decrypt(encrypted); console.log(uncrypted) // Now a simple check to see if the round-trip worked. if (uncrypted == $('#input').val()) { alert('It works!!!'); } else { alert('Something went wrong....'); } }); }); </script> <label for="privkey">Private Key</label><br/> <textarea id="privkey" rows="15" cols="65">-----BEGIN PRIVATE KEY----- MIIEvgIBADANBgkqhkiG9w0BAQEFAASCBKgwggSkAgEAAoIBAQDkaTKbAERvJGE0 jGsdPXUI1FpO1uDkBkuuQU4LRv0Quw9r8j+fVNkN9rZVXMV7MiGOgb80Z0k9zRxZ 5KWOqMnSlrpyO3WjhFpDJeSmqZ4wLMFwmxrr31AjabD5Nkf9dQ7RiEIuM49g27+M 3OFvdIPcLgCyXnkl8FwBceBs38QbCXY5MrwlZr13yWZnyj6fbbG8t4atAzJ6bnj3 FZuvynC3QnMaVi6YnTIlBOUOHtqt/jsUTOCWkwKqkZh+RZF2fx3IFkSpJAOMgT5p jSnfEJkK5E4JJHobLo/dFO0J7Gve+qb/lfJ9UpnZe78N1TAvbJiNZoN22ghbuIAW M5qqIqOzAgMBAAECggEBAItUJFtqoVQOpADy+s/+UirNpjzbVJmjwXyNN3cnmW0g PjsBrY+aqUCcUwLlMU2B+fg86w6jRokdWgL3t4m7Kkl8SkUuQgc5z/mP3tdPNkB6 vJDc/GIPeYnwidSrKOTSB/UGoiAesYJK6aCaiCV9tIWVxjUH7eyXnvf+qAChyrUW PG/FirLyYmz1yRG99VKKE+iEIzemGSswU0DI0bwTFQ0MunLeJf0EdT20XppNwnl4 uoRgOBpMkW02vxDDWke2YIpk128KFRtPE3zF7W+Prb3ifMuQHSqDdqTgZA5+G3A9 D+lwczy95+0mIBpJ8rKQGjJ51ZT5WVMET9+Hb9+nUIECgYEA9NluRzIi9tZxwQa2 KdU8WAtWZZQZfG18mSFg8/QYrAGF2TyLAW0mEIe7nQXxPzm50HdpxTJCkUrXGm3u hfPayx18H4oVVYRepSSfV+xe7wdogJWV6i5h/LaZsiTk1O8vF9Cwc3yUyVoMtKsg yVcsONOzo/Kg/vwejQJb1C8dNvMCgYEA7tAewjA25vDmfiWZ0lrWKlwGQZ97+pMU X+N12DWxL1Lvi6jBKXlK+Eiz19Qm/mBz9RxrDDY4/o0IjtTxdOh5thDaiqIcnqQn PiBpm7zbheZOlPBGjFJ1vwueIWvqbx9vcqHik/4xHwuFNwQ+YCSpVpVoqrgoN/h/ fX5+hKm1kEECgYEAzn69UZAICtLKNveZE+jBLqPJJnvjjpur1F1hLfzz/cR/BLnZ pcdOrew7Hu+PCTp+6kB7VJLRr0VF6gVCf3gsUta4AsVqvqeXRoF/XSB84+wEh0Ug nNKnUwEQ2DvjPW3G8rfOyGcN+E5YntogGY3KPtbUDvWmL8WjYlrV5Toi0l8CgYAQ Ujr37JGkAOzPzEQSA1FFvdpTm9G+U1T+JK6GI01DvbhPZC4nZnnAND/OTVqI4hCq vNF4GTCV/Q+Lq3QBGG5RCh/Vf7TTBscD0PVGxoZ+RTozpaQ8rNoNP38EK7ru80gL npK8qI+03nWxR+H3cin8l+N6X3GoOZyE+CMvb+XPwQKBgEeDjwTWxVhH/uksO3pw MgbHjauD6AjuW9jc2a7ngFCWSQxQ3+xK1Spn6pbVdLPiBgInxCIl8d6S1yFU0Uan iZHgy4fs1hdJRSuJ6qydqSwlS2C+gDpyY8ye0i+jq5VYYhKcpJCrCgaQGbleuaUd ldp7v1FD8uyeemknGA35f6Id -----END PRIVATE KEY-----</textarea><br/> <label for="pubkey">Public Key</label><br/> <textarea id="pubkey" rows="15" cols="65">-----BEGIN PUBLIC KEY----- MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA5GkymwBEbyRhNIxrHT11 CNRaTtbg5AZLrkFOC0b9ELsPa/I/n1TZDfa2VVzFezIhjoG/NGdJPc0cWeSljqjJ 0pa6cjt1o4RaQyXkpqmeMCzBcJsa699QI2mw+TZH/XUO0YhCLjOPYNu/jNzhb3SD 3C4Asl55JfBcAXHgbN/EGwl2OTK8JWa9d8lmZ8o+n22xvLeGrQMyem549xWbr8pw t0JzGlYumJ0yJQTlDh7arf47FEzglpMCqpGYfkWRdn8dyBZEqSQDjIE+aY0p3xCZ CuROCSR6Gy6P3RTtCexr3vqm/5XyfVKZ2Xu/DdUwL2yYjWaDdtoIW7iAFjOaqiKj swIDAQAB -----END PUBLIC KEY-----</textarea><br/> <label for="input">Text to encrypt:</label><br/> <textarea id="input" name="input" type="text" rows=4 cols=70>This is a test!</textarea><br/> <input id="testme" type="button" value="Test Me!!!" /><br/> </div> </body> </html>其中的公钥和私钥都是上面PHP代码中生成的,这边好像只有公钥加密,私钥解密。拿到其中打印出的加密后的数据,尝试在PHP中进行解密,可以看到也能解密成功。代码如下:<?php class Rsa { public $privateKey = '-----BEGIN PRIVATE KEY----- MIIEvgIBADANBgkqhkiG9w0BAQEFAASCBKgwggSkAgEAAoIBAQDkaTKbAERvJGE0 jGsdPXUI1FpO1uDkBkuuQU4LRv0Quw9r8j+fVNkN9rZVXMV7MiGOgb80Z0k9zRxZ 5KWOqMnSlrpyO3WjhFpDJeSmqZ4wLMFwmxrr31AjabD5Nkf9dQ7RiEIuM49g27+M 3OFvdIPcLgCyXnkl8FwBceBs38QbCXY5MrwlZr13yWZnyj6fbbG8t4atAzJ6bnj3 FZuvynC3QnMaVi6YnTIlBOUOHtqt/jsUTOCWkwKqkZh+RZF2fx3IFkSpJAOMgT5p jSnfEJkK5E4JJHobLo/dFO0J7Gve+qb/lfJ9UpnZe78N1TAvbJiNZoN22ghbuIAW M5qqIqOzAgMBAAECggEBAItUJFtqoVQOpADy+s/+UirNpjzbVJmjwXyNN3cnmW0g PjsBrY+aqUCcUwLlMU2B+fg86w6jRokdWgL3t4m7Kkl8SkUuQgc5z/mP3tdPNkB6 vJDc/GIPeYnwidSrKOTSB/UGoiAesYJK6aCaiCV9tIWVxjUH7eyXnvf+qAChyrUW PG/FirLyYmz1yRG99VKKE+iEIzemGSswU0DI0bwTFQ0MunLeJf0EdT20XppNwnl4 uoRgOBpMkW02vxDDWke2YIpk128KFRtPE3zF7W+Prb3ifMuQHSqDdqTgZA5+G3A9 D+lwczy95+0mIBpJ8rKQGjJ51ZT5WVMET9+Hb9+nUIECgYEA9NluRzIi9tZxwQa2 KdU8WAtWZZQZfG18mSFg8/QYrAGF2TyLAW0mEIe7nQXxPzm50HdpxTJCkUrXGm3u hfPayx18H4oVVYRepSSfV+xe7wdogJWV6i5h/LaZsiTk1O8vF9Cwc3yUyVoMtKsg yVcsONOzo/Kg/vwejQJb1C8dNvMCgYEA7tAewjA25vDmfiWZ0lrWKlwGQZ97+pMU X+N12DWxL1Lvi6jBKXlK+Eiz19Qm/mBz9RxrDDY4/o0IjtTxdOh5thDaiqIcnqQn PiBpm7zbheZOlPBGjFJ1vwueIWvqbx9vcqHik/4xHwuFNwQ+YCSpVpVoqrgoN/h/ fX5+hKm1kEECgYEAzn69UZAICtLKNveZE+jBLqPJJnvjjpur1F1hLfzz/cR/BLnZ pcdOrew7Hu+PCTp+6kB7VJLRr0VF6gVCf3gsUta4AsVqvqeXRoF/XSB84+wEh0Ug nNKnUwEQ2DvjPW3G8rfOyGcN+E5YntogGY3KPtbUDvWmL8WjYlrV5Toi0l8CgYAQ Ujr37JGkAOzPzEQSA1FFvdpTm9G+U1T+JK6GI01DvbhPZC4nZnnAND/OTVqI4hCq vNF4GTCV/Q+Lq3QBGG5RCh/Vf7TTBscD0PVGxoZ+RTozpaQ8rNoNP38EK7ru80gL npK8qI+03nWxR+H3cin8l+N6X3GoOZyE+CMvb+XPwQKBgEeDjwTWxVhH/uksO3pw MgbHjauD6AjuW9jc2a7ngFCWSQxQ3+xK1Spn6pbVdLPiBgInxCIl8d6S1yFU0Uan iZHgy4fs1hdJRSuJ6qydqSwlS2C+gDpyY8ye0i+jq5VYYhKcpJCrCgaQGbleuaUd ldp7v1FD8uyeemknGA35f6Id -----END PRIVATE KEY-----'; public $publicKey = '-----BEGIN PUBLIC KEY----- MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA5GkymwBEbyRhNIxrHT11 CNRaTtbg5AZLrkFOC0b9ELsPa/I/n1TZDfa2VVzFezIhjoG/NGdJPc0cWeSljqjJ 0pa6cjt1o4RaQyXkpqmeMCzBcJsa699QI2mw+TZH/XUO0YhCLjOPYNu/jNzhb3SD 3C4Asl55JfBcAXHgbN/EGwl2OTK8JWa9d8lmZ8o+n22xvLeGrQMyem549xWbr8pw t0JzGlYumJ0yJQTlDh7arf47FEzglpMCqpGYfkWRdn8dyBZEqSQDjIE+aY0p3xCZ CuROCSR6Gy6P3RTtCexr3vqm/5XyfVKZ2Xu/DdUwL2yYjWaDdtoIW7iAFjOaqiKj swIDAQAB -----END PUBLIC KEY-----'; public function __construct() { } public function publicEncrypt($data, $publicKey) { openssl_public_encrypt($data, $encrypted, $publicKey); return $encrypted; } public function publicDecrypt($data, $publicKey) { openssl_public_decrypt($data, $decrypted, $publicKey); return $decrypted; } public function privateEncrypt($data, $privateKey) { openssl_private_encrypt($data, $encrypted, $privateKey); return $encrypted; } public function privateDecrypt($data, $privateKey) { openssl_private_decrypt($data, $decrypted, $privateKey); return $decrypted; } } $rsa = new Rsa(); // 使用公钥加密的内容 $str = 'IUMBGcLwJECdxUu3LMbeEhGQdoRjCLqFwfZQBO/Odh3tClbq76Tva7yYqTVxexXLmZ3uY8DrOk/XwcVVRr6g9rBnv/zxBxUShCdN0CwkoguvI+6Oju2aUBlM4FhUp+gmasa5YfqylEp1RpsVAp67GMGlxZvp0ekfhFXkjSqAguPd7dKq5YjftP12xOyuJHAzzg7U+eHxffxnneKqXkK7QrfQD6VrLpbYmayPSjMza/RbjXF+d85UeUZUaF25PZ7Y7kD4Yo7/hY/L6peeOkI5//tpl6U4QY9VsFsjAbIpNMsZuNjE/cZ57Kc5WScPsmy0o9wsp5DUEJmu+YYmr6adoA=='; $str = base64_decode($str); $pubstr = $rsa->publicDecrypt($str, $rsa->publicKey); echo "公钥解密:\n", $pubstr, "\n"; $privstr = $rsa->privateDecrypt($str, $rsa->privateKey); echo "私钥解密:\n", $privstr, "\n"; 参考资料百度百科:非对称加密: https://baike.baidu.com/item/%E9%9D%9E%E5%AF%B9%E7%A7%B0%E5%8A%A0%E5%AF%86/9874417?fr=aladdinphp加密扩展: https://www.php.net/manual/zh/book.openssl.php
【PHP】RSA非对称加密解密 PHP服务端与客户端交互或者提供开放API时,通常需要对敏感的数据进行加密,这时候rsa非对称加密就能派上用处了。举个通俗易懂的例子,假设我们再登录一个网站,发送账号和密码,请求被拦截了。密码没加密,那攻击者就直接拿到了密码,这是最搓的。密码加密了,是不可逆加密,那攻击者只需要模拟那个请求即可登录。密码加密了,是可逆加密,其中携带有时间等参数,后台可以根据时间等参数来判断是否有效,但因为是在前端加密,其加密方式也能在代码中找到,找到加密方式就可以得出解密方式。但是如果我们使用非对称加密就可以避免以上问题。非对称加密算法需要两个密钥来进行加密和解密,这两个秘钥是公开密钥(public key,简称公钥)和私有密钥(private key,简称私钥)。工作过程如下,甲乙之间使用非对称加密的方式完成了重要信息的安全传输。乙方生成一对密钥(公钥和私钥)并将公钥向其它方公开。得到该公钥的甲方使用该密钥对机密信息进行加密后再发送给乙方。乙方再用自己保存的另一把专用密钥(私钥)对加密后的信息进行解密。乙方只能用其专用密钥(私钥)解密由对应的公钥加密后的信息。在传输过程中,即使攻击者截获了传输的密文,并得到了乙的公钥,也无法破解密文,因为只有乙的私钥才能解密密文。同样,如果乙要回复加密信息给甲,那么需要甲先公布甲的公钥给乙用于加密,甲自己保存甲的私钥用于解密。在非对称加密中使用的主要算法有:RSA、Elgamal、背包算法、Rabin、D-H、ECC(椭圆曲线加密算法)等。下面我们通过一个例子来说明如何用PHP来实现RSA的加密解密。<?php class Rsa { public $privateKey = ''; public $publicKey = ''; public function __construct() { $resource = openssl_pkey_new(); openssl_pkey_export($resource, $this->privateKey); $detail = openssl_pkey_get_details($resource); $this->publicKey = $detail['key']; } public function publicEncrypt($data, $publicKey) { openssl_public_encrypt($data, $encrypted, $publicKey); return $encrypted; } public function publicDecrypt($data, $publicKey) { openssl_public_decrypt($data, $decrypted, $publicKey); return $decrypted; } public function privateEncrypt($data, $privateKey) { openssl_private_encrypt($data, $encrypted, $privateKey); return $encrypted; } public function privateDecrypt($data, $privateKey) { openssl_private_decrypt($data, $decrypted, $privateKey); return $decrypted; } } $rsa = new Rsa(); echo "公钥:\n", $rsa->publicKey, "\n"; echo "私钥:\n", $rsa->privateKey, "\n"; // 使用公钥加密 $str = $rsa->publicEncrypt('hello', $rsa->publicKey); // 这里使用base64是为了不出现乱码,默认加密出来的值有乱码 $str = base64_encode($str); echo "公钥加密(base64处理过):\n", $str, "\n"; $str = base64_decode($str); $pubstr = $rsa->publicDecrypt($str, $rsa->publicKey); echo "公钥解密:\n", $pubstr, "\n"; $privstr = $rsa->privateDecrypt($str, $rsa->privateKey); echo "私钥解密:\n", $privstr, "\n"; // 使用私钥加密 $str = $rsa->privateEncrypt('world', $rsa->privateKey); // 这里使用base64是为了不出现乱码,默认加密出来的值有乱码 $str = base64_encode($str); echo "私钥加密(base64处理过):\n", $str, "\n"; $str = base64_decode($str); $pubstr = $rsa->publicDecrypt($str, $rsa->publicKey); echo "公钥解密:\n", $pubstr, "\n"; $privstr = $rsa->privateDecrypt($str, $rsa->privateKey); echo "私钥解密:\n", $privstr, "\n"; 大家执行一下可以看到公钥加密的数据,只有私钥能解密,反之亦然,私钥加密的数据只有公钥能解码。这是PHP端的实现,可用在第三方跟平台之间的数据传输,但如果是前端传到后端该怎么办呢,搜索了一下,发现了这个库https://github.com/travist/jsencrypt使用jsencrypt加密解密的例子如下:<!DOCTYPE html> <html> <head> <title>JSEncrypt Example</title> <base id="basetag" href="/jsencrypt-2.3.0/"> <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <meta name="viewport" content="width=device-width, initial-scale=1.0"> <script src="jquery.js"></script> <script type="text/javascript" src="bin/jsencrypt.js"></script> </head> <body> <div class="container"> <script type="text/javascript"> // Call this code when the page is done loading. $(function() { // Run a quick encryption/decryption when they click. $('#testme').click(function() { // Encrypt with the public key... var encrypt = new JSEncrypt(); encrypt.setPublicKey($('#pubkey').val()); var encrypted = encrypt.encrypt($('#input').val()); console.log(encrypted) // Decrypt with the private key... var decrypt = new JSEncrypt(); decrypt.setPrivateKey($('#privkey').val()); var uncrypted = decrypt.decrypt(encrypted); console.log(uncrypted) // Now a simple check to see if the round-trip worked. if (uncrypted == $('#input').val()) { alert('It works!!!'); } else { alert('Something went wrong....'); } }); }); </script> <label for="privkey">Private Key</label><br/> <textarea id="privkey" rows="15" cols="65">-----BEGIN PRIVATE KEY----- MIIEvgIBADANBgkqhkiG9w0BAQEFAASCBKgwggSkAgEAAoIBAQDkaTKbAERvJGE0 jGsdPXUI1FpO1uDkBkuuQU4LRv0Quw9r8j+fVNkN9rZVXMV7MiGOgb80Z0k9zRxZ 5KWOqMnSlrpyO3WjhFpDJeSmqZ4wLMFwmxrr31AjabD5Nkf9dQ7RiEIuM49g27+M 3OFvdIPcLgCyXnkl8FwBceBs38QbCXY5MrwlZr13yWZnyj6fbbG8t4atAzJ6bnj3 FZuvynC3QnMaVi6YnTIlBOUOHtqt/jsUTOCWkwKqkZh+RZF2fx3IFkSpJAOMgT5p jSnfEJkK5E4JJHobLo/dFO0J7Gve+qb/lfJ9UpnZe78N1TAvbJiNZoN22ghbuIAW M5qqIqOzAgMBAAECggEBAItUJFtqoVQOpADy+s/+UirNpjzbVJmjwXyNN3cnmW0g PjsBrY+aqUCcUwLlMU2B+fg86w6jRokdWgL3t4m7Kkl8SkUuQgc5z/mP3tdPNkB6 vJDc/GIPeYnwidSrKOTSB/UGoiAesYJK6aCaiCV9tIWVxjUH7eyXnvf+qAChyrUW PG/FirLyYmz1yRG99VKKE+iEIzemGSswU0DI0bwTFQ0MunLeJf0EdT20XppNwnl4 uoRgOBpMkW02vxDDWke2YIpk128KFRtPE3zF7W+Prb3ifMuQHSqDdqTgZA5+G3A9 D+lwczy95+0mIBpJ8rKQGjJ51ZT5WVMET9+Hb9+nUIECgYEA9NluRzIi9tZxwQa2 KdU8WAtWZZQZfG18mSFg8/QYrAGF2TyLAW0mEIe7nQXxPzm50HdpxTJCkUrXGm3u hfPayx18H4oVVYRepSSfV+xe7wdogJWV6i5h/LaZsiTk1O8vF9Cwc3yUyVoMtKsg yVcsONOzo/Kg/vwejQJb1C8dNvMCgYEA7tAewjA25vDmfiWZ0lrWKlwGQZ97+pMU X+N12DWxL1Lvi6jBKXlK+Eiz19Qm/mBz9RxrDDY4/o0IjtTxdOh5thDaiqIcnqQn PiBpm7zbheZOlPBGjFJ1vwueIWvqbx9vcqHik/4xHwuFNwQ+YCSpVpVoqrgoN/h/ fX5+hKm1kEECgYEAzn69UZAICtLKNveZE+jBLqPJJnvjjpur1F1hLfzz/cR/BLnZ pcdOrew7Hu+PCTp+6kB7VJLRr0VF6gVCf3gsUta4AsVqvqeXRoF/XSB84+wEh0Ug nNKnUwEQ2DvjPW3G8rfOyGcN+E5YntogGY3KPtbUDvWmL8WjYlrV5Toi0l8CgYAQ Ujr37JGkAOzPzEQSA1FFvdpTm9G+U1T+JK6GI01DvbhPZC4nZnnAND/OTVqI4hCq vNF4GTCV/Q+Lq3QBGG5RCh/Vf7TTBscD0PVGxoZ+RTozpaQ8rNoNP38EK7ru80gL npK8qI+03nWxR+H3cin8l+N6X3GoOZyE+CMvb+XPwQKBgEeDjwTWxVhH/uksO3pw MgbHjauD6AjuW9jc2a7ngFCWSQxQ3+xK1Spn6pbVdLPiBgInxCIl8d6S1yFU0Uan iZHgy4fs1hdJRSuJ6qydqSwlS2C+gDpyY8ye0i+jq5VYYhKcpJCrCgaQGbleuaUd ldp7v1FD8uyeemknGA35f6Id -----END PRIVATE KEY-----</textarea><br/> <label for="pubkey">Public Key</label><br/> <textarea id="pubkey" rows="15" cols="65">-----BEGIN PUBLIC KEY----- MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA5GkymwBEbyRhNIxrHT11 CNRaTtbg5AZLrkFOC0b9ELsPa/I/n1TZDfa2VVzFezIhjoG/NGdJPc0cWeSljqjJ 0pa6cjt1o4RaQyXkpqmeMCzBcJsa699QI2mw+TZH/XUO0YhCLjOPYNu/jNzhb3SD 3C4Asl55JfBcAXHgbN/EGwl2OTK8JWa9d8lmZ8o+n22xvLeGrQMyem549xWbr8pw t0JzGlYumJ0yJQTlDh7arf47FEzglpMCqpGYfkWRdn8dyBZEqSQDjIE+aY0p3xCZ CuROCSR6Gy6P3RTtCexr3vqm/5XyfVKZ2Xu/DdUwL2yYjWaDdtoIW7iAFjOaqiKj swIDAQAB -----END PUBLIC KEY-----</textarea><br/> <label for="input">Text to encrypt:</label><br/> <textarea id="input" name="input" type="text" rows=4 cols=70>This is a test!</textarea><br/> <input id="testme" type="button" value="Test Me!!!" /><br/> </div> </body> </html>其中的公钥和私钥都是上面PHP代码中生成的,这边好像只有公钥加密,私钥解密。拿到其中打印出的加密后的数据,尝试在PHP中进行解密,可以看到也能解密成功。代码如下:<?php class Rsa { public $privateKey = '-----BEGIN PRIVATE KEY----- MIIEvgIBADANBgkqhkiG9w0BAQEFAASCBKgwggSkAgEAAoIBAQDkaTKbAERvJGE0 jGsdPXUI1FpO1uDkBkuuQU4LRv0Quw9r8j+fVNkN9rZVXMV7MiGOgb80Z0k9zRxZ 5KWOqMnSlrpyO3WjhFpDJeSmqZ4wLMFwmxrr31AjabD5Nkf9dQ7RiEIuM49g27+M 3OFvdIPcLgCyXnkl8FwBceBs38QbCXY5MrwlZr13yWZnyj6fbbG8t4atAzJ6bnj3 FZuvynC3QnMaVi6YnTIlBOUOHtqt/jsUTOCWkwKqkZh+RZF2fx3IFkSpJAOMgT5p jSnfEJkK5E4JJHobLo/dFO0J7Gve+qb/lfJ9UpnZe78N1TAvbJiNZoN22ghbuIAW M5qqIqOzAgMBAAECggEBAItUJFtqoVQOpADy+s/+UirNpjzbVJmjwXyNN3cnmW0g PjsBrY+aqUCcUwLlMU2B+fg86w6jRokdWgL3t4m7Kkl8SkUuQgc5z/mP3tdPNkB6 vJDc/GIPeYnwidSrKOTSB/UGoiAesYJK6aCaiCV9tIWVxjUH7eyXnvf+qAChyrUW PG/FirLyYmz1yRG99VKKE+iEIzemGSswU0DI0bwTFQ0MunLeJf0EdT20XppNwnl4 uoRgOBpMkW02vxDDWke2YIpk128KFRtPE3zF7W+Prb3ifMuQHSqDdqTgZA5+G3A9 D+lwczy95+0mIBpJ8rKQGjJ51ZT5WVMET9+Hb9+nUIECgYEA9NluRzIi9tZxwQa2 KdU8WAtWZZQZfG18mSFg8/QYrAGF2TyLAW0mEIe7nQXxPzm50HdpxTJCkUrXGm3u hfPayx18H4oVVYRepSSfV+xe7wdogJWV6i5h/LaZsiTk1O8vF9Cwc3yUyVoMtKsg yVcsONOzo/Kg/vwejQJb1C8dNvMCgYEA7tAewjA25vDmfiWZ0lrWKlwGQZ97+pMU X+N12DWxL1Lvi6jBKXlK+Eiz19Qm/mBz9RxrDDY4/o0IjtTxdOh5thDaiqIcnqQn PiBpm7zbheZOlPBGjFJ1vwueIWvqbx9vcqHik/4xHwuFNwQ+YCSpVpVoqrgoN/h/ fX5+hKm1kEECgYEAzn69UZAICtLKNveZE+jBLqPJJnvjjpur1F1hLfzz/cR/BLnZ pcdOrew7Hu+PCTp+6kB7VJLRr0VF6gVCf3gsUta4AsVqvqeXRoF/XSB84+wEh0Ug nNKnUwEQ2DvjPW3G8rfOyGcN+E5YntogGY3KPtbUDvWmL8WjYlrV5Toi0l8CgYAQ Ujr37JGkAOzPzEQSA1FFvdpTm9G+U1T+JK6GI01DvbhPZC4nZnnAND/OTVqI4hCq vNF4GTCV/Q+Lq3QBGG5RCh/Vf7TTBscD0PVGxoZ+RTozpaQ8rNoNP38EK7ru80gL npK8qI+03nWxR+H3cin8l+N6X3GoOZyE+CMvb+XPwQKBgEeDjwTWxVhH/uksO3pw MgbHjauD6AjuW9jc2a7ngFCWSQxQ3+xK1Spn6pbVdLPiBgInxCIl8d6S1yFU0Uan iZHgy4fs1hdJRSuJ6qydqSwlS2C+gDpyY8ye0i+jq5VYYhKcpJCrCgaQGbleuaUd ldp7v1FD8uyeemknGA35f6Id -----END PRIVATE KEY-----'; public $publicKey = '-----BEGIN PUBLIC KEY----- MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA5GkymwBEbyRhNIxrHT11 CNRaTtbg5AZLrkFOC0b9ELsPa/I/n1TZDfa2VVzFezIhjoG/NGdJPc0cWeSljqjJ 0pa6cjt1o4RaQyXkpqmeMCzBcJsa699QI2mw+TZH/XUO0YhCLjOPYNu/jNzhb3SD 3C4Asl55JfBcAXHgbN/EGwl2OTK8JWa9d8lmZ8o+n22xvLeGrQMyem549xWbr8pw t0JzGlYumJ0yJQTlDh7arf47FEzglpMCqpGYfkWRdn8dyBZEqSQDjIE+aY0p3xCZ CuROCSR6Gy6P3RTtCexr3vqm/5XyfVKZ2Xu/DdUwL2yYjWaDdtoIW7iAFjOaqiKj swIDAQAB -----END PUBLIC KEY-----'; public function __construct() { } public function publicEncrypt($data, $publicKey) { openssl_public_encrypt($data, $encrypted, $publicKey); return $encrypted; } public function publicDecrypt($data, $publicKey) { openssl_public_decrypt($data, $decrypted, $publicKey); return $decrypted; } public function privateEncrypt($data, $privateKey) { openssl_private_encrypt($data, $encrypted, $privateKey); return $encrypted; } public function privateDecrypt($data, $privateKey) { openssl_private_decrypt($data, $decrypted, $privateKey); return $decrypted; } } $rsa = new Rsa(); // 使用公钥加密的内容 $str = 'IUMBGcLwJECdxUu3LMbeEhGQdoRjCLqFwfZQBO/Odh3tClbq76Tva7yYqTVxexXLmZ3uY8DrOk/XwcVVRr6g9rBnv/zxBxUShCdN0CwkoguvI+6Oju2aUBlM4FhUp+gmasa5YfqylEp1RpsVAp67GMGlxZvp0ekfhFXkjSqAguPd7dKq5YjftP12xOyuJHAzzg7U+eHxffxnneKqXkK7QrfQD6VrLpbYmayPSjMza/RbjXF+d85UeUZUaF25PZ7Y7kD4Yo7/hY/L6peeOkI5//tpl6U4QY9VsFsjAbIpNMsZuNjE/cZ57Kc5WScPsmy0o9wsp5DUEJmu+YYmr6adoA=='; $str = base64_decode($str); $pubstr = $rsa->publicDecrypt($str, $rsa->publicKey); echo "公钥解密:\n", $pubstr, "\n"; $privstr = $rsa->privateDecrypt($str, $rsa->privateKey); echo "私钥解密:\n", $privstr, "\n"; 参考资料百度百科:非对称加密: https://baike.baidu.com/item/%E9%9D%9E%E5%AF%B9%E7%A7%B0%E5%8A%A0%E5%AF%86/9874417?fr=aladdinphp加密扩展: https://www.php.net/manual/zh/book.openssl.php -
 【PHP】cURL error 60: SSL certificate unable to get local issuer certificate 导致该问题的原因在于没有配置curl.cainfo,该配置位于php.ini中解决方案:1 下载cacert.pemhttps://curl.haxx.se/ca/cacert.pem2 配置 php.ini[curl] ; A default value for the CURLOPT_CAINFO option. This is required to be an ; absolute path. curl.cainfo = 【你的绝对路径】记得重启php
【PHP】cURL error 60: SSL certificate unable to get local issuer certificate 导致该问题的原因在于没有配置curl.cainfo,该配置位于php.ini中解决方案:1 下载cacert.pemhttps://curl.haxx.se/ca/cacert.pem2 配置 php.ini[curl] ; A default value for the CURLOPT_CAINFO option. This is required to be an ; absolute path. curl.cainfo = 【你的绝对路径】记得重启php -
![【mysql】解决报错:SQLSTATE[HY000] [2054] The server requested authentication method unknown to the client](https://static.richerdyoung.com/blog/image/lazyload.jpg) 【mysql】解决报错:SQLSTATE[HY000] [2054] The server requested authentication method unknown to the client 错误信息提示SQLSTATE[HY000] [2054] The server requested authentication method unknown to the client原因由于MySQL 8默认使用了新的密码验证插件:caching_sha2_password,而低版本的PHP版本中所带的mysqlnd无法支持这种验证。故报“请求客户端未知的身份验证方法”。解决方案一可以通过phpinfo()函数了解当前安装的PHP是否支持caching_sha2_password方案二更改加密方式 alter user 'root'@'localhost' identified with mysql_native_password by '123456'; flush privileges;
【mysql】解决报错:SQLSTATE[HY000] [2054] The server requested authentication method unknown to the client 错误信息提示SQLSTATE[HY000] [2054] The server requested authentication method unknown to the client原因由于MySQL 8默认使用了新的密码验证插件:caching_sha2_password,而低版本的PHP版本中所带的mysqlnd无法支持这种验证。故报“请求客户端未知的身份验证方法”。解决方案一可以通过phpinfo()函数了解当前安装的PHP是否支持caching_sha2_password方案二更改加密方式 alter user 'root'@'localhost' identified with mysql_native_password by '123456'; flush privileges; -
 【html】Layui 静态表格复选框全选 html<table class="layui-table" > <thead> <tr> <th><input type="checkbox" name="" lay-skin="primary" lay-filter="allChoose"></th> <th>id</th> </tr> </thead> <tbody> {foreach $data_list as $key=>$vo } <tr> <td><input type="checkbox" name="id_array[]" value="{$vo.id}" lay-skin="primary" lay-filter="itemChoose" ></td> <td>{$vo.id}</td> </tr> {/foreach} </tbody> </table> js <script> layui.use(['form', 'layedit','jquery','element','table'], function() { var form = layui.form; table = layui.table; form.render(); //全选or 取消全选 form.on('checkbox(allChoose)', function(data){ //所有 var all_child = $(data.elem).parents('table').find('tbody input[type="checkbox"]'); //data.elem.checked 值为 true 或者 false all_child.each(function(index, item){ item.checked = data.elem.checked; }); form.render('checkbox'); //获取已选中 var checked_child = $(data.elem).parents('table').find('tbody input[type="checkbox"]:checked'); layer.msg('选中了:'+ checked_child.length + ' 个'); //获取选中的值 var arr_box = []; checked_child.each(function() { arr_box.push($(this).val()); }); console.log(arr_box.toString()); }); //全选和部分选中时候,表头全选按钮的样式变化 form.on('checkbox(itemChoose)', function (data) { var sib = $(data.elem).parents('table').find('tbody input[type="checkbox"]:checked').length; var total = $(data.elem).parents('table').find('tbody input[type="checkbox"]').length; if (sib == total) { $(data.elem).parents('table').find('thead input[type="checkbox"]').prop("checked", true); } else { $(data.elem).parents('table').find('thead input[type="checkbox"]').prop("checked",false); } form.render('checkbox'); //获取已选中 var child = $(data.elem).parents('table').find('tbody input[type="checkbox"]:checked'); layer.msg('选中了:'+ child.length + ' 个'); //获取选中的值 var arr_box = []; child.each(function() { arr_box.push($(this).val()); }); console.log(arr_box.toString()); }); }); </script>
【html】Layui 静态表格复选框全选 html<table class="layui-table" > <thead> <tr> <th><input type="checkbox" name="" lay-skin="primary" lay-filter="allChoose"></th> <th>id</th> </tr> </thead> <tbody> {foreach $data_list as $key=>$vo } <tr> <td><input type="checkbox" name="id_array[]" value="{$vo.id}" lay-skin="primary" lay-filter="itemChoose" ></td> <td>{$vo.id}</td> </tr> {/foreach} </tbody> </table> js <script> layui.use(['form', 'layedit','jquery','element','table'], function() { var form = layui.form; table = layui.table; form.render(); //全选or 取消全选 form.on('checkbox(allChoose)', function(data){ //所有 var all_child = $(data.elem).parents('table').find('tbody input[type="checkbox"]'); //data.elem.checked 值为 true 或者 false all_child.each(function(index, item){ item.checked = data.elem.checked; }); form.render('checkbox'); //获取已选中 var checked_child = $(data.elem).parents('table').find('tbody input[type="checkbox"]:checked'); layer.msg('选中了:'+ checked_child.length + ' 个'); //获取选中的值 var arr_box = []; checked_child.each(function() { arr_box.push($(this).val()); }); console.log(arr_box.toString()); }); //全选和部分选中时候,表头全选按钮的样式变化 form.on('checkbox(itemChoose)', function (data) { var sib = $(data.elem).parents('table').find('tbody input[type="checkbox"]:checked').length; var total = $(data.elem).parents('table').find('tbody input[type="checkbox"]').length; if (sib == total) { $(data.elem).parents('table').find('thead input[type="checkbox"]').prop("checked", true); } else { $(data.elem).parents('table').find('thead input[type="checkbox"]').prop("checked",false); } form.render('checkbox'); //获取已选中 var child = $(data.elem).parents('table').find('tbody input[type="checkbox"]:checked'); layer.msg('选中了:'+ child.length + ' 个'); //获取选中的值 var arr_box = []; child.each(function() { arr_box.push($(this).val()); }); console.log(arr_box.toString()); }); }); </script>



![微信支付报错dial tcp [240e:e1:a900:50::49]:443: connect: network is unreachable](https://richerdyoung.com/usr/themes/Joe/assets/thumb/23.jpg)




![【mysql】解决报错:SQLSTATE[HY000] [2054] The server requested authentication method unknown to the client](https://richerdyoung.com/usr/themes/Joe/assets/thumb/15.jpg)
